|
|
|
DMT SQL Decryptor 2.4

Screenshot |
DMT SQL Decryptor is a powerful database objects decrypt tools for Microsoft SQL Server 2000, 2005. Using it you can quickly decrypt stored procedures, views, user defined functions, table triggers, database triggers and server triggers in an easy to use Enterprise Manager-like graphical interface. DMT SQL Decryptor allows for easy viewing and editing of encrypted code, of any size, with T-SQL syntax highlighting and multiple format exportation.
Download
| Order
| Broken Link Report
| More Info
Support Languages:
English
Install Support: Install and Uninstall
Keywords:
Application Server Defined, Application Server Web Server, Asp Sql Server, Buy Sql Server, Decrypt, Decrypt Sql, Decryptor, Defined Benefit Retirement ..., Ibm Web Server, Knowledge Management Defined, Procedure, Sms Server, Sql Server, Sql Server 2005, Trigger, Unencryption, User Defined Function, View, Web Server Application Server, Xp Web Server |
|
|
DMT SQL Decryptor Comments
|
Join to DMT SQL Decryptor discussion at FileGets! Let's see what our visitors think about it and write your own opinion! Rate this software to support developers or to make them work better! Also please write here if you want to see any additional features in this software.
Notice: * - required fields
|
|
DMT SQL Decryptor Also Mentioned
|
| Clone DVD III 3.0 |
 |
| Clone DVD III is an outstanding DVD Copy application and one of the few available that includes the CSS decryptor . The CSS decryptor is what allows you to copy copy-protected DVDs. |
| 1st DVD Cloner 2.5 |
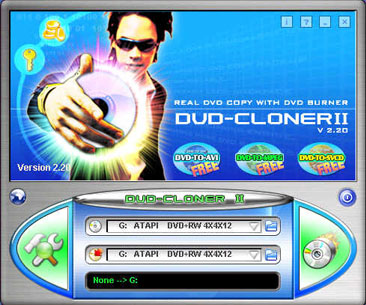 |
| 1st DVD Cloner --- Genuine clone DVD to DVD software! 1st DVD Cloner Make copying DVD's
with your DVD burner a reality and the DVD-R/RW, DVD+R/RW copied by 1st DVD Cloner is the
same as... |
| Icon Lock-iT XP 3.3 |
 |
| Icon Lock-iT XP, portable file encryption, locking, and security for Windows XP, 2000, NT Desktop files. Portable data storage security for iPod and flash drives. Secure, safe password protection.... |
| I-Cipher AP 2.2.2 |
 |
| I-Cipher is ideal for encryption/decryption of virtually any size of images, scanned documents, or electronic art. It proves to be an invaluable tool for image protection against unauthorized use... |
|
|
|